FinTech Trends Newsletter Week 3rd July – 7th June 2017

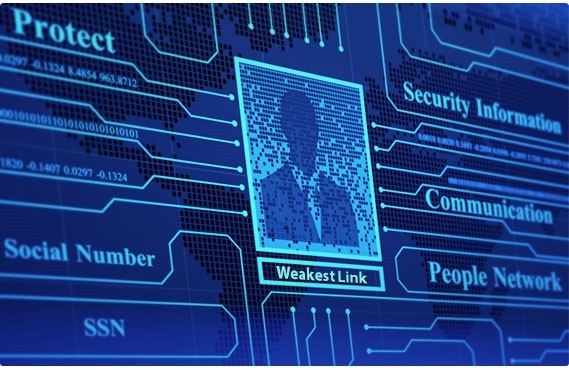
Education is the Key with IT Security: Preying on human weaknesses, not computer weaknesses
Where the exposures lie: – It’s late in the day on a Friday afternoon, and an urgent email hits a back-office employee’s inbox. As the employee clambers to get ready for the market-close and head off for the weekend, it looks like the portfolio manager for an important client needs him to wire $150,000USD to a bank in Grand Cayman.
His colleagues are all busy dealing with other matters, and, since he’s keen to be reactive to this key client’s request, he follows the wire instructions in the email to complete the transfer in good time.
Bad move.
Unfortunately, in the rush to complete the transaction request, the employ- ee neglected to see the carefully crafted and well-disguised typo in the do-main name of the email address. That message wasn’t from a portfolio man- ager. It was from a phishing hacker. Minutes later, after the theft was de- tected, the employee called the bank to reverse the wire, but the money was already two steps away, never to be seen again.
The reality is today, more often than not, these nightmare scenarios involve social engineering, that preys on human weaknesses, not computer weakness. That’s because, even with sophisticated perimeter security and vigilant monitoring in place, the greatest vulnerability, sadly, re- mains the people who use your IT systems to conduct transactions and access sensitive data.
This fictional investment firm didn’t need more firewalls, more passwords, or more encryption. What it did need was an internal culture of security – an ongoing, firm wide commitment to defining and adhering to careful, thoughtful policies that reduce or eliminate
“people vulnerabilities” through assessments, awareness, and above all education, something we at Storm IT Financial advocate highly and can help financial firms with training seminars.
To avoid becoming the victim of a phishing hack like in the scenario above, it is important to:
1) Slow down to ensure you are acting professionally 2) Check the sender email address as well as “to” and “cc” fields 3) O nly click on
links and at t achment s t hat you are exp ect ing 4) Be wary of generic greetings 5) Check for improper spelling 6) Be wary of urgent re- quests for personal information
What is an Internal Culture of Security? Sometimes all the firewalls in the world won’t stop the most damaging attacks as the breach is human error which can only be stopped by education. In many instances, employees are “holding the door open” to hackers.
Unintentional employee threats include weak or shared passwords, unsecure equipment, improper disposal of hard copy documentation, visitor access to networks, and feeling rushed. Some intentional or malicious employee threats include disgruntled employees and those in search of monetary gain.
So how do we strengthen these people-centric security vulnerabilities? Firms must create an internal culture of security. And, above all else, that needs to start from the very top of the firm (people who, ironically, due to the volume and sensitivity of the information they access and the distractions their fast-paced lives encounter, can sometimes represent the greatest source of vulnerabilities to infor- mation security). It’s essential that they visibly and fully commit their unwavering support to your efforts to improve security.
We hope that you now understand and are more aware the importance of security culture and what it means to have a culture of secu- rity in your firm. Education is the key.
For more information on Hedge Fund, Asset Management, Private Equity & Alternative Investment cyber security & firewall, data back- up, disaster recovery & failover advice, cloud & IT Services, feel free to contact Storm IT Financial.

Storm IT Financial FinTech News & Trends picks: Week 3rd July – 7th July 2017
How Azure Security detects attacks using cyber threat intelligence
Microsoft Azure goal to constantly improve security detection and alerting capabilities:
Buy-side study released conducted by BNY Mellon & Pricewaterhouse- Coopers focused around liquidity and collateral concerns
Hedge funds are looking to add new prime brokers & service providers, according to buy side study…:
https://www.bnymellon.com/_global-assets/pdf/our-thinking/collateral-the-new-performance-driver.pdf
Is cloud the future for core banking?
In just three years from now, every new core banking system that goes live will do so in the cloud:
https://www.finextra.com/blogposting/14252/is-cloud-the-future-for-core-banking
Germany says cyber threat greater than expected, more firms affected
The threat posed to German firms by recent cyber attacks was greater than expected with some firms halting production…:
http://uk.reuters.com/article/us-cyber-attack-ukraine-germany- idUKKBN19S1EU
Financial services firms are automating certain jobs while hiring to fill digital skills gaps
It’s no secret that financial services firms on both the sell-side & buy-side are automating as many roles as they can:
Cyber attacks are prompting a boost in cybersecurity M&A, figures reveal
Both strategic buyers and private equity firms are showing a renewed interest in cybersecurity acquisitions…:
http://www.cityam.com/267995/cyber-attacks-prompting-boost-cybersecurity-ma-figures
MiFID II – Are we nearly there yet?
The Financial Conduct Authority’s (FCA) publication of its final policy statement on the implementation of MiFID II early this week…:
Application security in the cloud: Who is responsible?
We’ve all heard about the benefits of cloud infrastruc- ture that paint cloud as the be all, end all for IT:
IT infrastructure spend is heading to the cloud
Spending on IT infrastructure for the cloud is climbing and may overtake traditional deployments by 2020:
Preqin: Emerging Hedge Funds Outperform Estab- lished Peers
New start up hedge funds outperform their more estab- lished peers in their first three years:
http://www.finalternatives.com/node/35453
Britain is a tech powerhouse leading the global revo- lution
Britain has seized the huge opportunities of the grow- ing tech industry:

